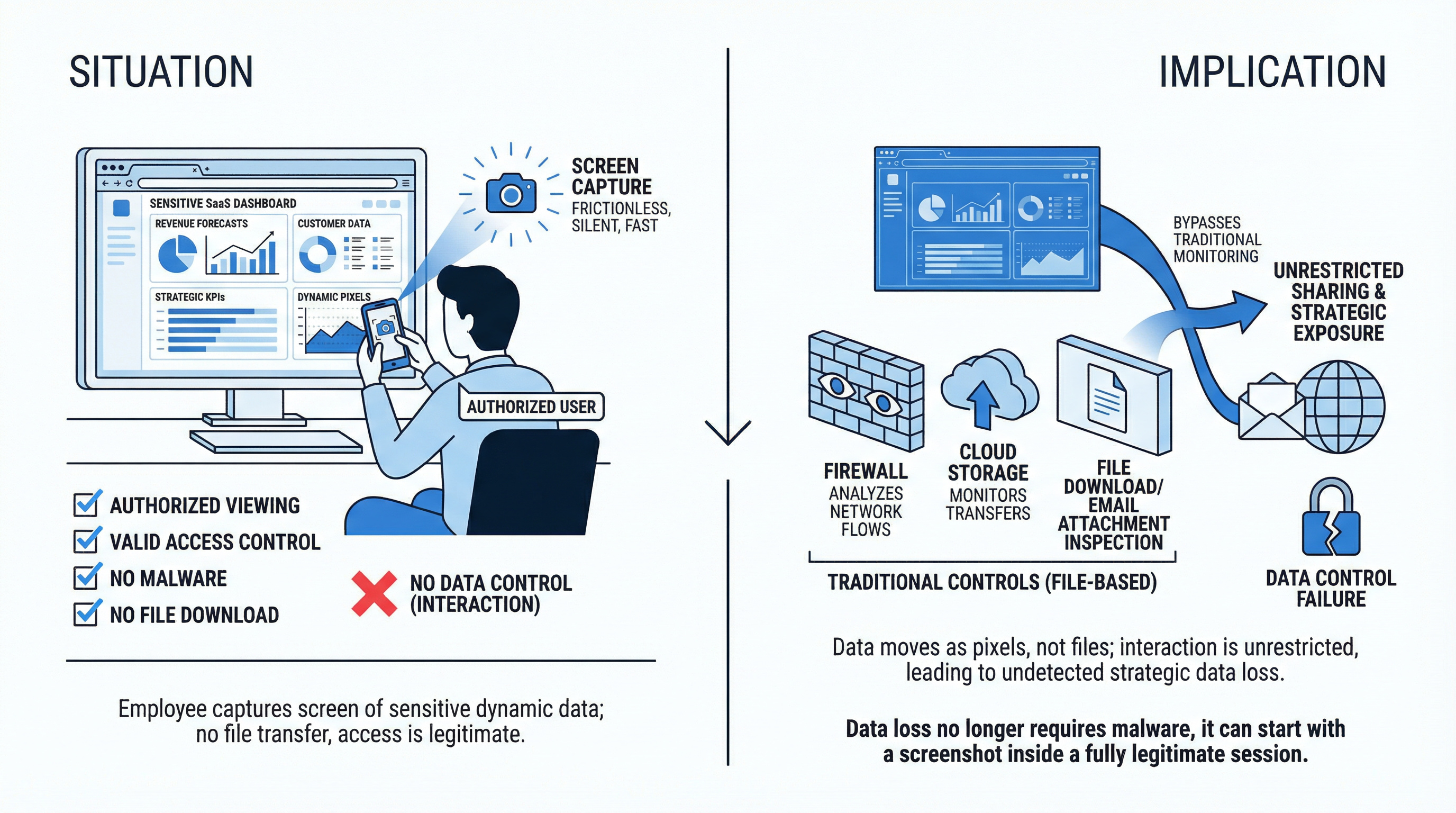
A sensitive SaaS dashboard was shared via screenshot, bypassing traditional file-based security controls entirely.

A sensitive SaaS dashboard displayed revenue forecasts, customer data, and strategic KPIs.
An employee captured the screen.
Shared the image externally.
No malware.
No file download.
No unusual outbound traffic.
No policy alert.
From a security perspective, everything looked normal.
Access control worked exactly as designed.
The user was authorized to view the dashboard.
What failed was data control.
The illusion of protection
Most security programs are built around files.
They monitor:
Data loss prevention tools inspect documents.
CASB tools look at SaaS traffic.
Firewalls analyze network flows.
But what happens when the data never leaves as a file?
Modern SaaS environments render sensitive information dynamically inside the browser:
Financial dashboards.
Customer intelligence platforms.
HR systems.
Board reporting portals.
Operational control panels.
There maybe no “download” button involved.
Just pixels on a screen.
And pixels are easy to capture.
The shift from files to interaction
In a SaaS-first enterprise, the browser is the workspace.
Critical business information is no longer stored in local folders.
It lives in live dashboards and web applications.
When an authorized user views that data, traditional controls assume the job is done.
The user is authenticated.
The role is correct.
The permissions are appropriate.
But access control is not the same as data control.
Access control answers:
Who can see this?
Data control answers:
What can they do with it once they see it?
There is a meaningful difference.
A screenshot bypasses file-based monitoring completely.
No file transfer to detect.
No attachment to scan.
No abnormal bandwidth spike.
Just a browser session with unrestricted interaction.
Why this risk is growing
Three structural changes have expanded this exposure:
SaaS centralization
More sensitive data is now delivered through web applications rather than downloadable reports.
Distributed work forces
Remote and hybrid employees work from diverse environments, increasing variability in device control.
Executive and partner access
High-valued dashboards are frequently accessed by executives, consultants, and external stakeholders.
The more valuable the data, the more attractive the target.
And screenshots are friction less.
They are fast.
They are silent.
They are rarely governed.
The governance gap
Many organizations believe they have strong controls because:
But none of these measures address interaction inside the browser session itself.
Can sensitive SaaS pages be screen captured?
Can high-risk dashboards be watermarked dynamically?
Can viewing behavior be monitored in real time?
Can session controls differentiate between standard users and privileged roles?
In most environments, the answer is no.
The browser is treated as a neutral viewing layer.
It is not.
It is the primary data interaction layer in modern enterprises.
Moving security to the work layer
If business-critical activity happens inside the browser, security must operate there as well.
Modern enterprise browser architecture allows organizations to:
This shifts enforcement from infrastructure to interaction.
From files to behavior.
From perimeter to session.
Why this matters at the executive Level
The most sensitive dashboards are often viewed by:
The impact of unauthorized disclosure at that level is not operational.
It is strategic.
And strategic exposure rarely begins with malware.
Sometimes it begins with a screenshot.
Rethinking what “Data Loss” means
Data loss no longer requires
It can happen inside a fully legitimate session.
The user was authorized.
The login was valid.
The permissions were correct.
But the interaction was unrestricted.
If your security strategy focuses primarily on controlling files and monitoring traffic, it may not reflect how data actually moves today.
In SaaS environments, data moves through interaction.
And interaction happens in the browser.
The question worth asking
If one of your most sensitive dashboards were viewed right now:
Access control is necessary.
It is not sufficient.
The browser is no longer just a window to applications.
It is the primary enforcement point for modern work.
If your organization has not evaluated interaction-level controls inside the browser,it may be time to reconsider where your real exposure lives.
Because sometimes, the breach does not start with malware.
It starts with a screenshot.
Strengthen your session and control framework - contact CySecPros for a confidential discussion.