We enable state-of-the-art cybersecurity vendors to establish a strong, credible, and cost-efficient presence in the Nordics (primarily), without the friction and capital burn of traditional expansion models.
We apply rigorous due diligence before representing any technology.
Our commitment to our enterprise customers means we engage only with solutions that deliver structural innovation and measurable business impact.

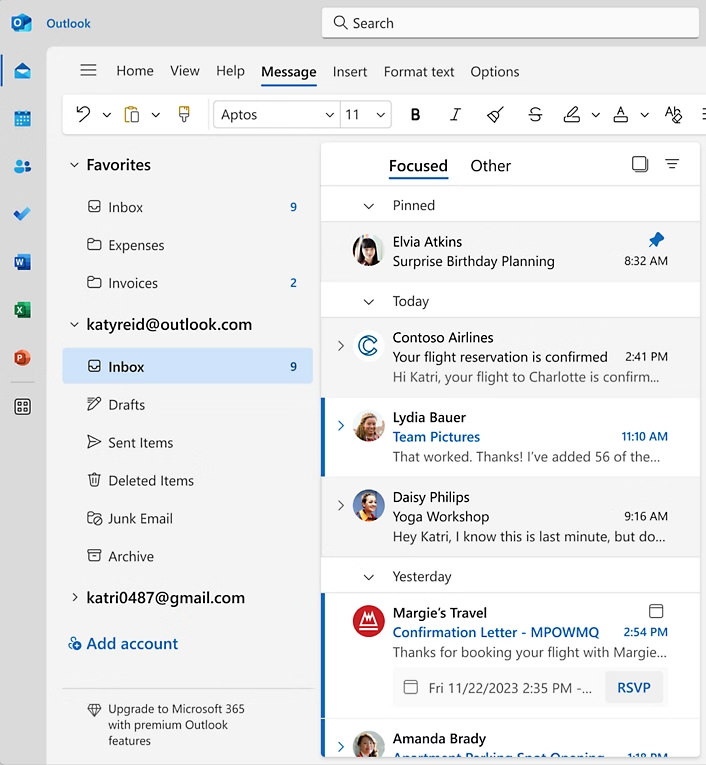
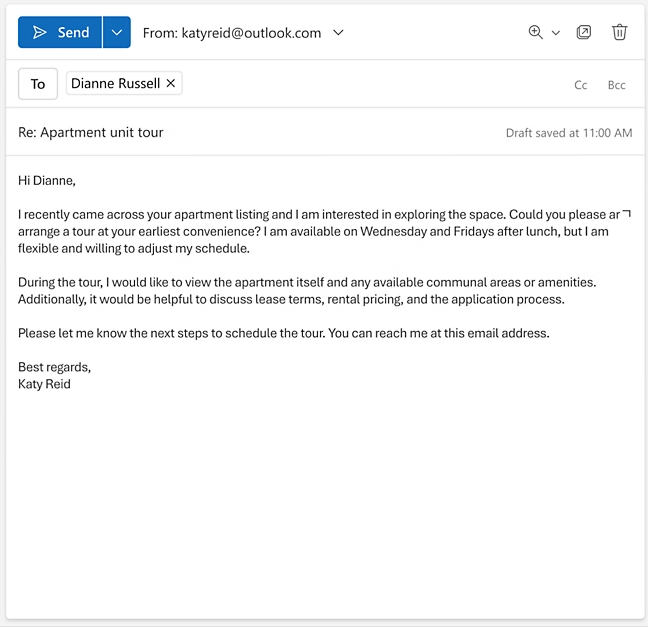
We are highly selective in the technologies we introduce to the Nordic enterprise and public sector market. A strong partnership typically looks likethis:
If you are serious about reducing structural risk and modernizing your security architecture, let’s start the conversation.