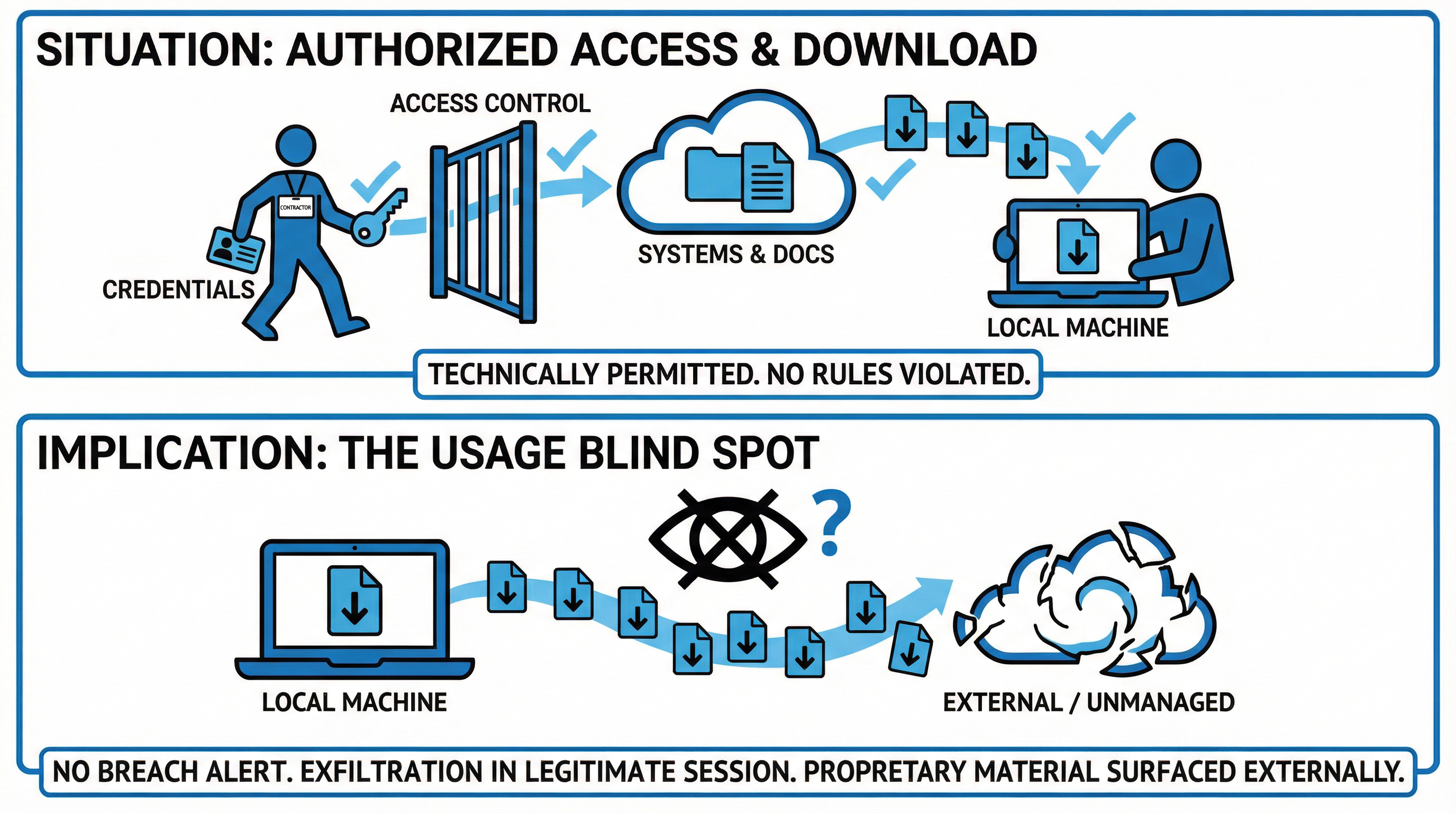
A contractor used approved access, followed policy, and triggered no alerts, yet sensitive data still left the organization.

The contractor followed policy.
He was provisioned access to specific systems.
He logged in using assigned credentials.
He accessed project documentation.
He downloaded files to complete his assignment.
Everything was technically permitted.
Two weeks later, his contract ended.
Months later, proprietary material surfaced externally.
There was no breach alert because no rule had been violated.
This is a common blind spot in SaaS-driven environments.
Access controls define who can log in and what they can see.
They rarely define what can be done with the data once accessed.
In distributed work environments with contractors and partners:
Can sensitive files be downloaded locally?
Can data be copied into un-managed applications?
Can screenshots or bulk exports occur without visibility?
Are session behaviors monitored for abnormal extraction patterns?
Data exfiltration often happens within legitimate sessions.
Trust-based access models do not scale across temporary roles and third-party relationships.
Security must evolve from access control to usage control.
If your organization collaborates heavily with contractors or external partners, it maybe time to evaluate how data movement is governed inside active sessions.
Reference cases -why it matters:
One of the most widely cited examples of authorized access leading to massive data exfiltration.
Snowden did not breach security systems.
He used legitimate privileges and downloaded data he could see.
Monitoring systems did not detect the scale of extraction until after the disclosure.
Why it fits your narrative
In 2023, two former employees leaked sensitive data from Tesla
In 2023, two former employees leaked sensitive data from Tesla, including personal information of more than 75,000 employees.
Investigations indicated that the individuals had legitimate access to the systems containing the data.
No external breach occurred.
Why it matters
The incident highlights that internal access to HR systems enabled full data extraction once trust in the user was assumed.
Strengthen your session and control framework - contact CySecPros for a confidential discussion.