Why restoring data is not enough — and why configuration governance defines real resilience.

In platforms such as Microsoft 365, resilience is typically associated with data protection. Organizations invest in backup strategies for mailboxes, documents, and collaboration content. Recovery plans are built around restoring files, messages, and records to ensure business continuity.
Configuration rarely receives the same structured attention.
Yet configuration is what governs the environment.
It determines:
Who can access what
Which policies are enforced
How identities authenticate
How privileged roles are assigned
How conditional access is applied
How security controls are configured
How compliance boundaries are defined and maintained
Data represents what the business produces.
Configuration defines how the business operates securely.
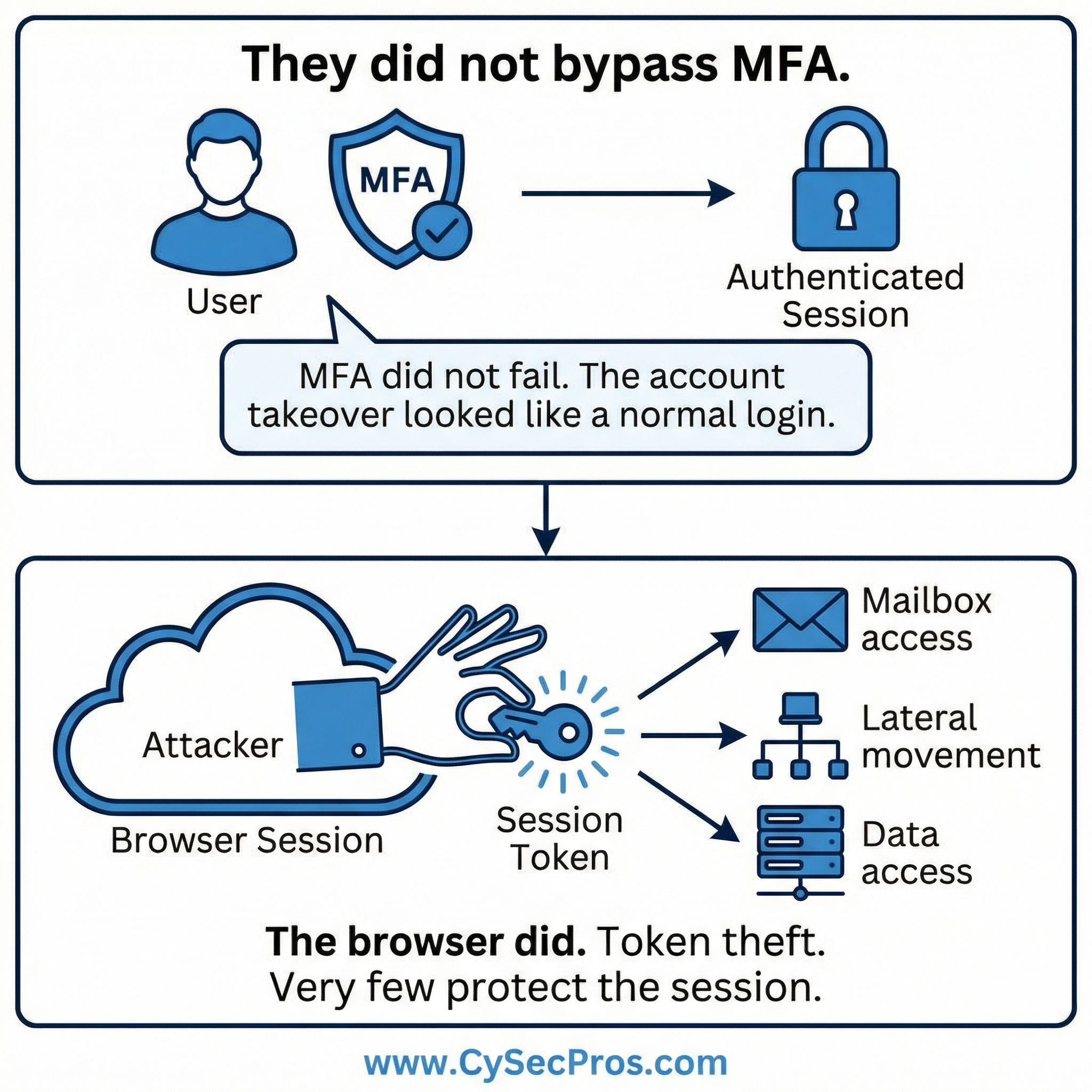
When a tenant is compromised, attackers do not limit themselves to extracting information. They often modify conditional access policies, adjust authentication requirements, create new privileged roles, disable monitoring settings, alter retention policies, or introduce backdoor accounts for persistence.
These changes may not be immediately visible.
They may not trigger urgent alarms.
But they weaken the integrity of the control framework.
Without a reliable and structured configuration backup, recovery becomes investigative rather than restorative. Security and IT teams must manually compare settings, determine what was altered, validate what was legitimate, and attempt to rebuild the original security posture from documentation, exports, or institutional memory.
This process is slow.
It is resource-intensive.
And it introduces uncertainty at the very moment the organization requires clarity.
Every hour spent reconstructing policies and permissions increases operational disruption, extends audit exposure, and amplifies executive risk.
True resilience requires more than stopping the attack and restoring data.
It requires the rapid restoration of governance state to a verified, trusted baseline.
With structured configuration backup and controlled recovery capabilities, organizations can quickly reestablish policy integrity, role assignments, and security controls. Instead of rebuilding manually, they can revert deliberately. Instead of guessing, they can restore with confidence.
Because stopping an attacker is only half the battle.
Restoring control is the other half.
Reference cases - why it matters
In many Microsoft 365 business email compromise cases, attackers do more than read mail.
They frequently modify tenant configurations such as:
Because these changes occur inside legitimate administrative controls, organizations often struggle to determine which configurations were altered during the compromise.
Recovery therefore requires:
Relevance
Even when email data is restored, security posture may remain compromised until configuration integrity is verified - without up to date tenant config. backup this becomes a huge task.
The SolarWinds supply chain attack allowed attackers to infiltrate numerous enterprise and government networks through compromised SolarWinds Orion updates.
Once inside environments, attackers:
Organizations impacted by the attack faced a major challenge: determining which configurations and trust relationships had been altered.
Many affected organizations ultimately rebuilt identity infrastructure and privileged access models rather than attempting piecemeal restoration.
Relevance
The attack illustrated how control-plane integrity becomes the primary recovery problem once attackers gain administrative access - without up to date tenant config. backup this becomes a huge task.
Strengthen your session and control framework - contact CySecPros for a confidential discussion.