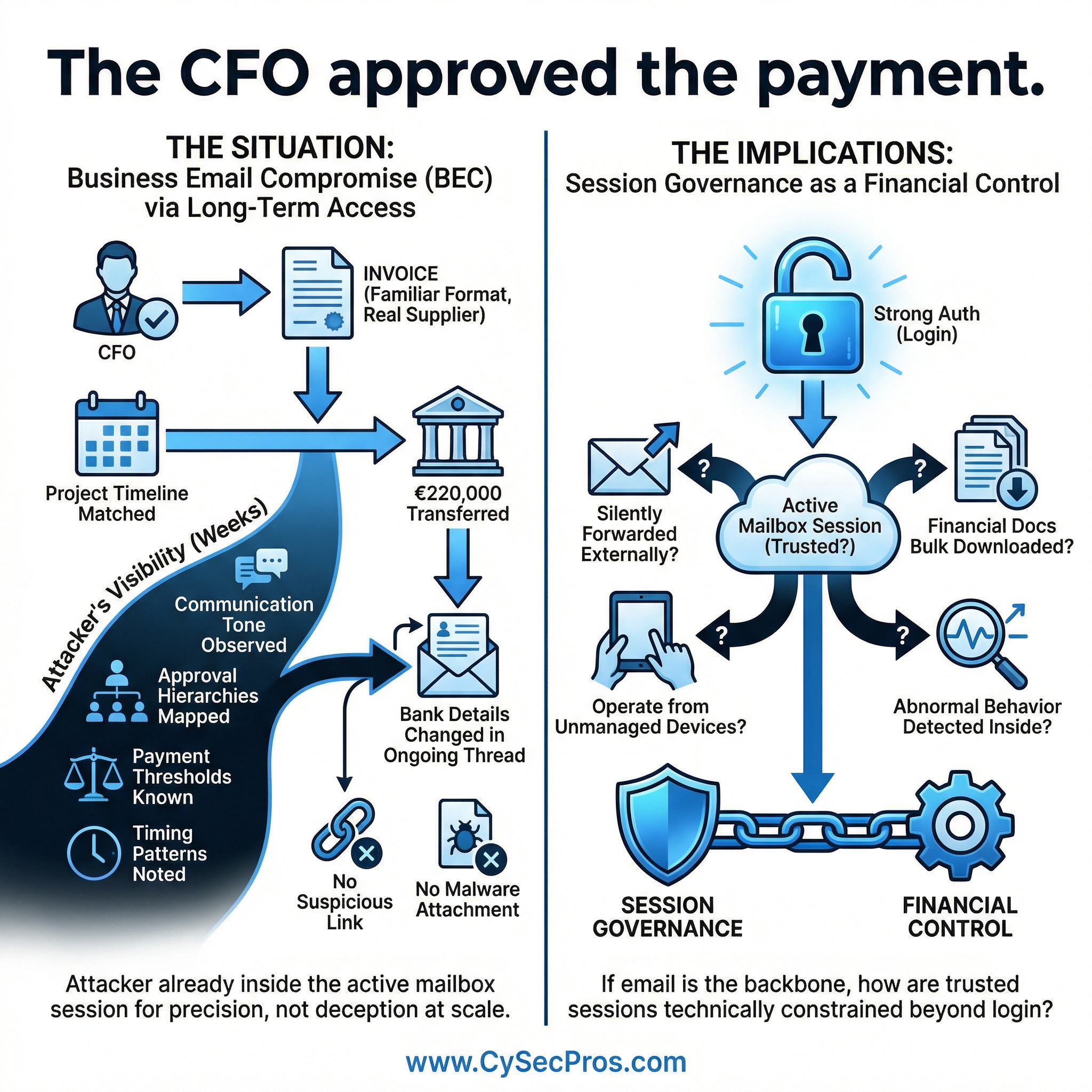
Business Email compromise through long-term mailbox session access, not phishing.

The CFO approved the payment.
The supplier was real.
The invoice format was familiar.
The project timeline matched expectations.
€220,000 transferred.
This was not a classic phishing attack.
It was business email compromise through long-term mailbox access.
The attacker had visibility for weeks.
They observed:
Communication tone between finance and operations.
Approval hierarchies.
Payment thresholds that required executive sign-off.
Timing patterns around month-end transfers.
When the right moment arrived, they changed banking details inside an ongoing email thread. No suspicious link was required. No malware attachment was delivered.
The attacker was already inside the mailbox session.
Modern Business Email Compromise (BEC) attacks are less about deception at scale and more about surveillance and precision.
Organizations typically protect login events with strong authentication controls. However, once a mailbox session is active:
Can emails be silently forwarded externally?
Can financial documents be bulk downloaded?
Can the session operate from unmanaged devices?
Is abnormal behavior detected inside the live session?
If email is the backbone of financial approval workflows, session governance becomes a financial control — not just a security control.
If your finance team depends entirely on trusted inbox sessions, it is worth asking how those sessions are technically constrained.
Reference cases - why it matters
In 2019, a subsidiary of Toyota Boshoku lost approximately $37 million in a sophisticated business email compromise.
Attackers impersonated a trusted business partner and requested payment for what appeared to be a legitimate transaction.
Investigations indicated the attackers had deep knowledge of internal payment procedures and supplier relationships, suggesting extended monitoring of communications.
Why it fits the scenario
The fraud succeeded because the attackers understood how financial approvals worked inside ongoing conversations.
Between 2013 and 2015, attacker Evaldas Rimasauskas orchestrated a large-scale BEC scheme targeting Google and Facebook.
The attacker impersonated a legitimate supplier and sent fraudulent invoices over time.
The scheme resulted in more than $100 million in payments being transferred before the fraud was detected.
Relevance
The attack relied on:
No technical exploitation was required — the payments were approved through normal operational channels.
Strengthen your session and control framework - contact CySecPros for a confidential discussion.