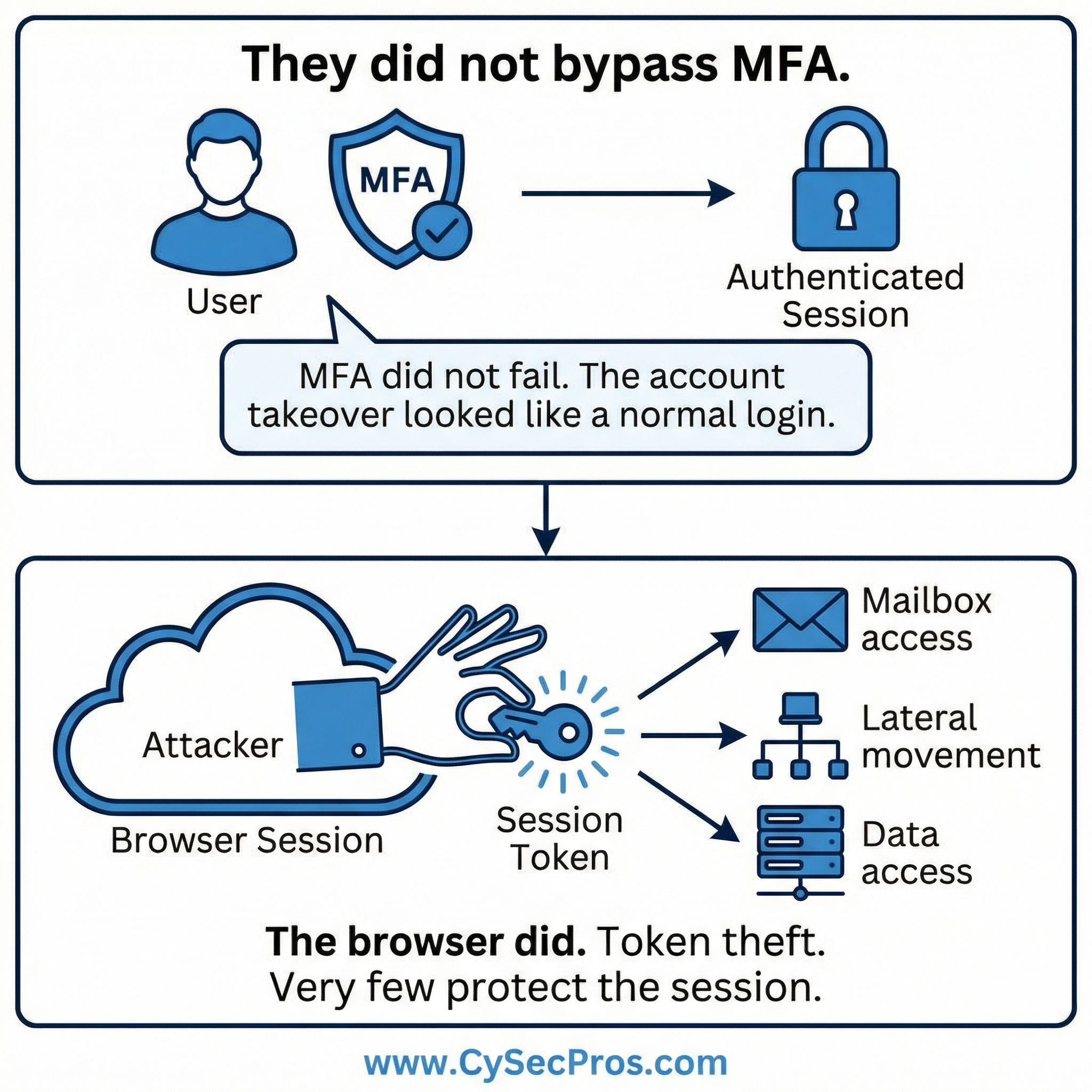
How modern account takeover works through stolen session tokens — even when MFA succeeds.

They did not bypass MFA.
There was no brute force attempt.
No password spraying campaign.
No MFA push fatigue attack.
The user authenticated successfully.
The multi-factor challenge was approved.
A session was established.
Then the attacker stole the session token.
From that moment forward, credentials were irrelevant. MFA was irrelevant.
The attacker simply replayed the authenticated session.
This is how modern account takeover works.
The security stack focuses heavily on identity:
Identity providers.
Conditional access.
Strong authentication policies.
But once authentication succeeds, the browser session often becomes implicitly trusted.
Session tokens stored locally can be extracted through malware, malicious browser extensions, or cross-site scripting. Once stolen, they can be replayed from another environment unless they are bound to device or browser context.
The result:
Mailbox rules created.
Sensitive conversations downloaded.
Privilege escalation initiated.
Lateral movement across SaaS applications.
Security logs show legitimate authentication and legitimate user behavior. There is no password reset event. No failed login pattern. No obvious anomaly.
MFA did not fail.
The session layer was never protected.
Most organizations secure identity at the door.
Few secure the room after the door is opened.
If your defensive model assumes that authentication equals trust for the duration of a session, that assumption deserves review.
Reference cases - why it matters
In 2023, attackers compromised the support environment of Okta.
The attackers obtained HAR files uploaded by customers for troubleshooting.
Those HAR files contained session tokens and authentication cookies.
Attackers used the tokens to:
Again:
Investigations revealed that attackers stole Outlook Web Access session tokens belonging to government officials.
The activity was attributed to a Chinese threat group tracked by Microsoft.
Attackers gained access to:
The attack replayed authenticated session tokens to access mailboxes without triggering MFA again.
Why it matters
This is one of the clearest modern examples of token replay bypassing MFA entirely
Strengthen your session and control framework - contact CySecPros for a confidential discussion.