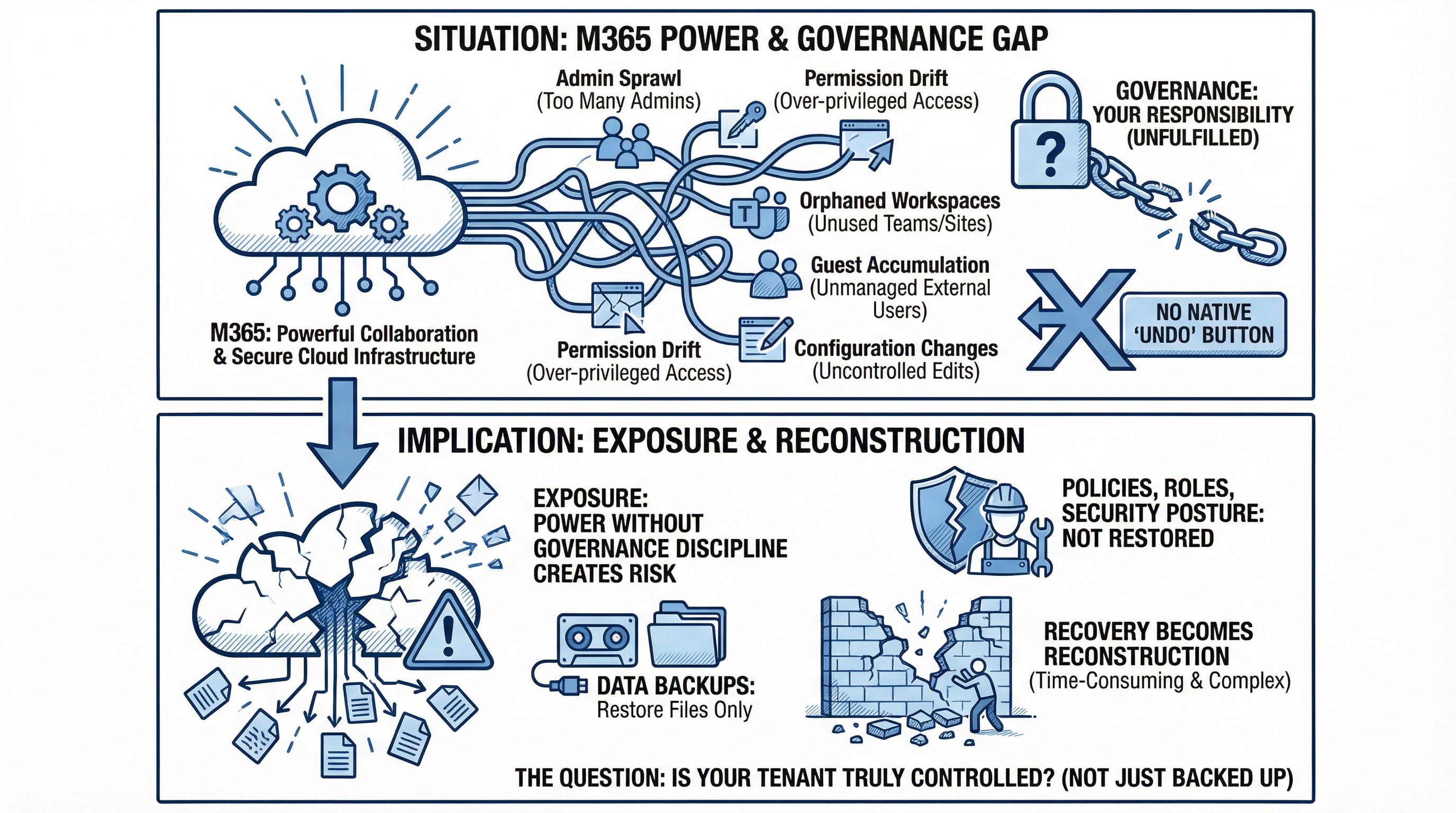
Microsoft 365 secures infrastructure, but without governance and configuration control, resilience quickly turns into risk exposure.

Microsoft365 has become the operational backbone of the enterprise. Identity,collaboration, security policy, compliance controls, and administrative roles all converge inside a single cloud tenant.
Most organizations back up their data.
Few protect their configuration.
When something goes wrong — whether through compromise, misconfiguration, or administrative error, data may still be intact. But if policies, role assignments, and security controls are altered, the environment itself becomes unstable.
And without a trusted baseline, recovery becomes reconstruction.
Configuration is what governs the environment
In Microsoft365, resilience is often equated with mailbox and file recovery.
But configuration defines how the platform operates securely.
It determines:
Configuration is not static. It evolves daily through policy updates, new projects, role changes, and platform enhancements.
Over time, that complexity compounds.
Large enterprises can accumulate hundreds of thousands of configuration settings across services. A minor change in one area can cascade into unintended consequences elsewhere.
Without centralized oversight, drift becomes inevitable.
When drift becomes exposure
Configuration drift rarely announces itself.
A policy is adjusted to solve an urgent issue.
A role is granted temporarily.
A setting is modified during troubleshooting.
Weeks later, no one remembers what changed.
In more severe scenarios, such as tenant compromise, attackers do not only access data. They modify controls. They weaken authentication requirements. They assign new administrative roles. They introduce persistence mechanisms.
If there is no structured configuration backup, the organization must determine:
Under pressure, that process is slow and uncertain.
Recovery shifts from controlled restoration to forensic investigation.
Operational downtime increases. Audit exposure widens. Executive confidence erodes.
Why native capabilities are not enough
Microsoft secures the infrastructure of the cloud.
Governance of configuration remains the organization’s responsibility.
There is no native, tenant-wide “undo” button for configuration changes. Data can be restored. Policies, role structures, and conditional access rules often can not be easily reverted without manual effort.
That gap creates risk.
True resilience requires:
Without these controls, even a contained incident can lead to prolonged operational instability.
From complexity to control
Effective configuration governance transforms Microsoft 365 from a reactive environment into a resilient one.
It enables organizations to:
Data recovery restores content.
Configuration recovery restores control.
And control is what protects the enterprise when disruption occurs.
Concerned about your ability to restore configuration and maintain governance integrity across your M365 environment? Engage with us for a confidential executive review of configuration resilience and risk posture.
Strengthen your session and control framework - contact CySecPros for a confidential discussion.