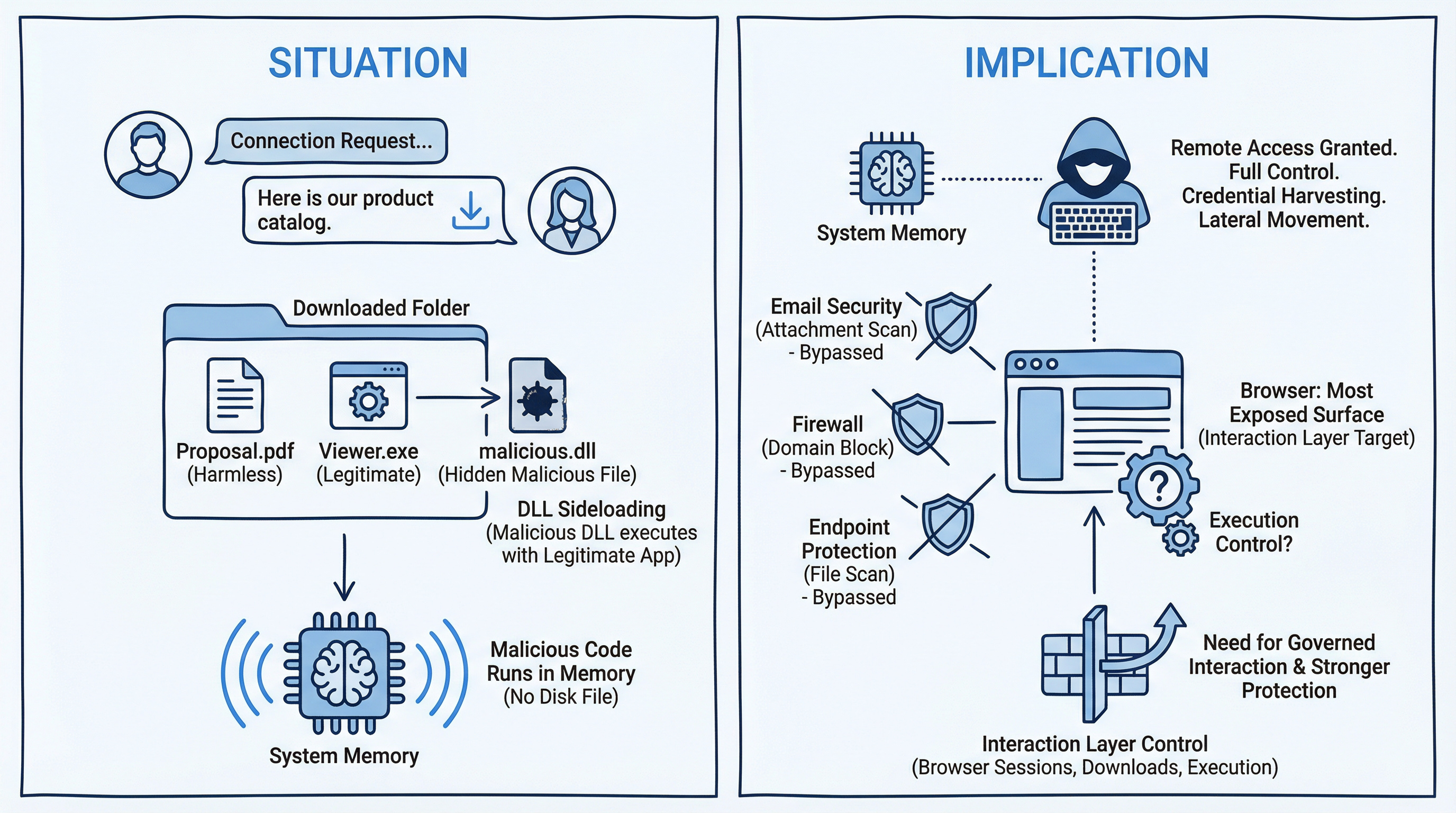
A malicious LinkedIn download uses DLL sideloading to execute silently and establish remote access.

LinkedIn is now the world’s fourth most impersonated brand in phishing attacks.
According to Check Point Research, 11 percent of global phishing attempts use the platform as bait.
The conversation begins innocently.
A connection request.
A short exchange.
A relevant discussion about partnership, recruitment, or collaboration.
Then comes the message:
“Here is our product catalog.”
“Please review the project proposal.”
The file appears harmless.
A PDF reader.
A standard document viewer.
Inside the same folder, however, sits a malicious file.
When the program launches, the hidden file executes automatically.
The technique is called DLL side loading.
Windows searches for required program files in the same directory as the application before checking system locations. Attackers exploit this behavior by placing a malicious file with the same name as a legitimate system component.
The result?
The malicious code runs in memory.
No obvious file written to disk.
No traditional antivirus alert.
No immediate red flag.
From there, the attacker gains remote access to the machine.
Full control.
Credential harvesting.
Lateral movement into corporate systems.
According to Check Point’s Threat Intelligence Report, Danish companies are exposed to an average of 1,334 cyberattack attempts per week.
According to PwC’s Global Digital Trust Insights, 32 percent of organizations have experienced a security incident within the past year.
And according to TDC Erhverv, a cyberattack can cost a small or medium-sized business up to 140,000 DKK per day in lost operations.
This shift is not accidental.
Attackers are moving toward platforms that feel trusted. Professional. Relevant.
Email security scans attachments.
Firewalls block known malicious domains.
Endpoint protection looks for suspicious executables.
But what happens when the download originates from a trusted social platform?
Who monitors what employees download through professional networking conversations?
Who controls how files execute once inside a legitimate browser session?
Modern attacks increasingly bypass perimeter defenses because they do not attack the perimeter.
They target interaction.
A trusted brand.
A professional dialogue.
A harmless-looking file.
If your defensive strategy focuses primarily on email gateways and network filtering, the browser may now be the most exposed surface in your environment.
The question is no longer whether employees will interact on LinkedIn.
They already are.
The question is whether those interactions are governed.
If this scenario feels plausible in your organization, it may be time to look closer at how browser sessions, downloads, and execution paths are controlled.
We are seeing this pattern accelerate across industries.
If you would like to explore what stronger protection at the interaction layer looks like, the conversation is worth having now.
It is understandable if you are thinking "how the ...........am I suppose to stop/block/prevent this?" - Contact us to explore how.
Reference cases - why it matters
1. Lazarus “Operation Dream Job”Campaign (H2)
The North Korean threat group Lazarus Group conducted a long-running campaign known as “Operation Dream Job.”
Attackers posed as recruiters on LinkedIn, contacting employees in aerospace,defense, and technology companies.
Victims received files such as:
The documents often contained malware loaders that deployed tools using DLL side loading techniques.
Once executed, attackers gained:
Why it fits the narrative
The attack began with a legitimate professional conversation on LinkedIn, not a suspicious email.
2. Operation In(ter)ception – Defense Industry Targeting (H2)
Another campaign known as Operation In(ter)ception targeted employees in aerospace and defense companies.
Attackers used fake recruiter profiles on LinkedIn to establish conversations before sending malicious documents.
The malware often relied on:
The goal was to gain long-term access to corporate environments and sensitive research data.
Why it fits the narrative
The attack began with a legitimate professional conversation on LinkedIn, not a suspicious email.
Strengthen your session and control framework - contact CySecPros for a confidential discussion.