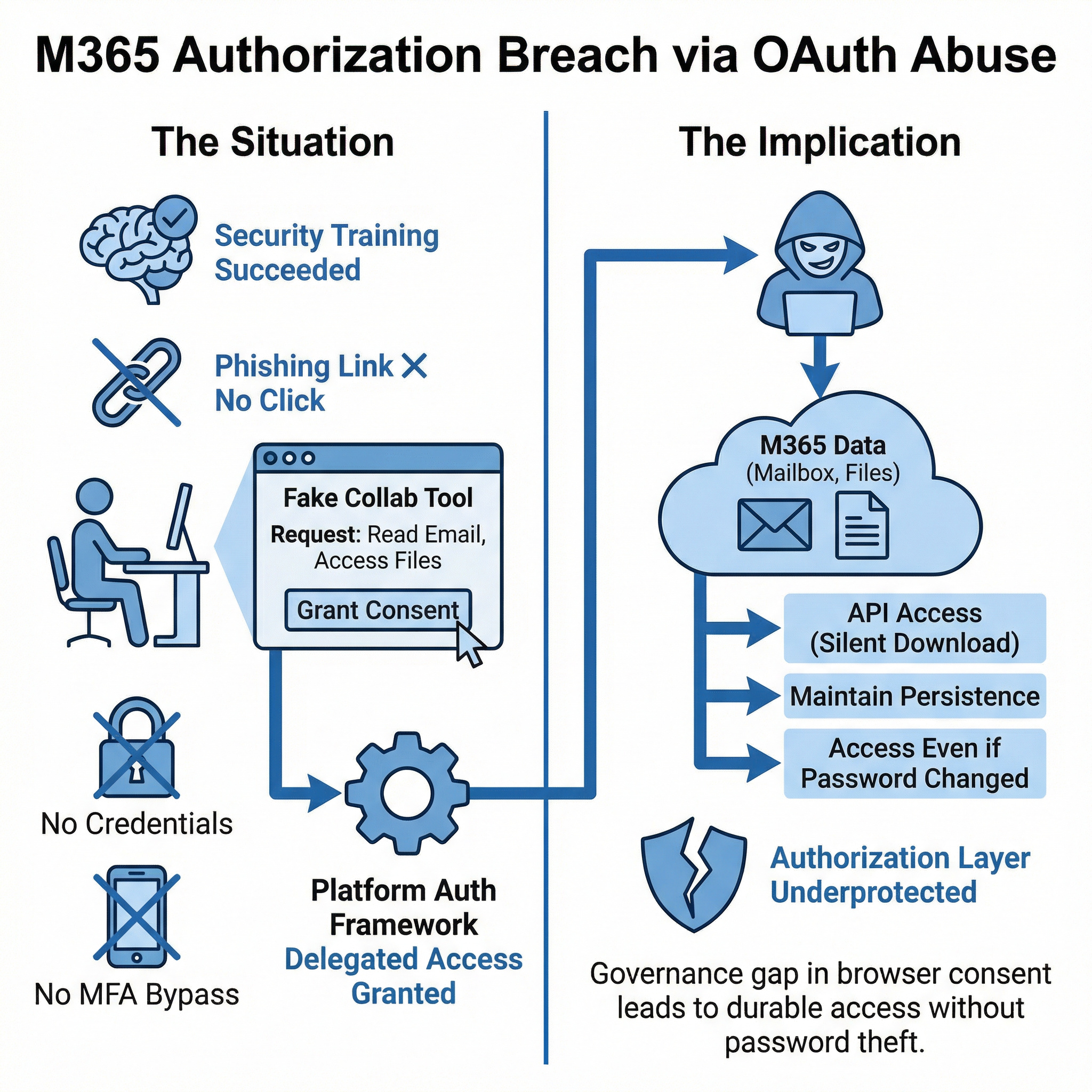
OAuth abuse and delegated SaaS access without credential theft.

Security awareness training succeeded.
No one clicked the phishing link.
Yet the breach still occurred.
The user received an OAuth consent prompt for what appeared to be a collaboration tool. It requested access to read email and access files.
The user approved the request.
No credentials were entered into a fake page.
No MFA was bypassed.
Instead, the attacker gained delegated access through the platform’s own authorization framework.
OAuth abuse is increasingly common because it leverages legitimate cloud functionality. Once consent is granted, the attacker can:
Access mailboxes through APIs.
Download files silently.
Maintain persistence even if passwords are changed.
Many organizations focus on credential theft prevention. Fewer tightly govern application consent and delegated permissions.
Questions worth asking:
Are users allowed to approve third-party SaaS integrations freely?
Are high-risk permissions flagged in real time?
Are consent flows restricted to sanctioned applications only?
Modern SaaS ecosystems are highly extensible by design. That flexibility is powerful - and risky.
If governance does not extend to in-browser consent actions, attackers can gain durable access without ever stealing a password.
If your SaaS security strategy centers only on authentication, the authorization layer may be under protected.
Reference cases - why it matters
The Russian threat actor Midnight Blizzard targeted organizations using OAuth application abuse to maintain persistence in cloud environments.
According to investigations by Microsoft, attackers attempted to:
Because OAuth tokens operate independently of passwords, the attackers could maintain access even after credentials were reset.
Relevance
This campaign highlights how OAuth permissions can create long-lived access paths that survive traditional credential remediation.
Security researchers and Microsoft have repeatedly documented consent phishing campaigns targeting Microsoft 365 tenants.
Attackers create malicious applications that request permissions such as:
Mail.ReadFiles.ReadWriteoffline_accessUsers receive a legitimate OAuth consent prompt that appears to be a collaboration or productivity application.
Once the user approves the request, the attacker gains:
Importantly:
Relevance
The compromise occurs through authorized delegated access granted by the user.
Strengthen your session and control framework - contact CySecPros for a confidential discussion.