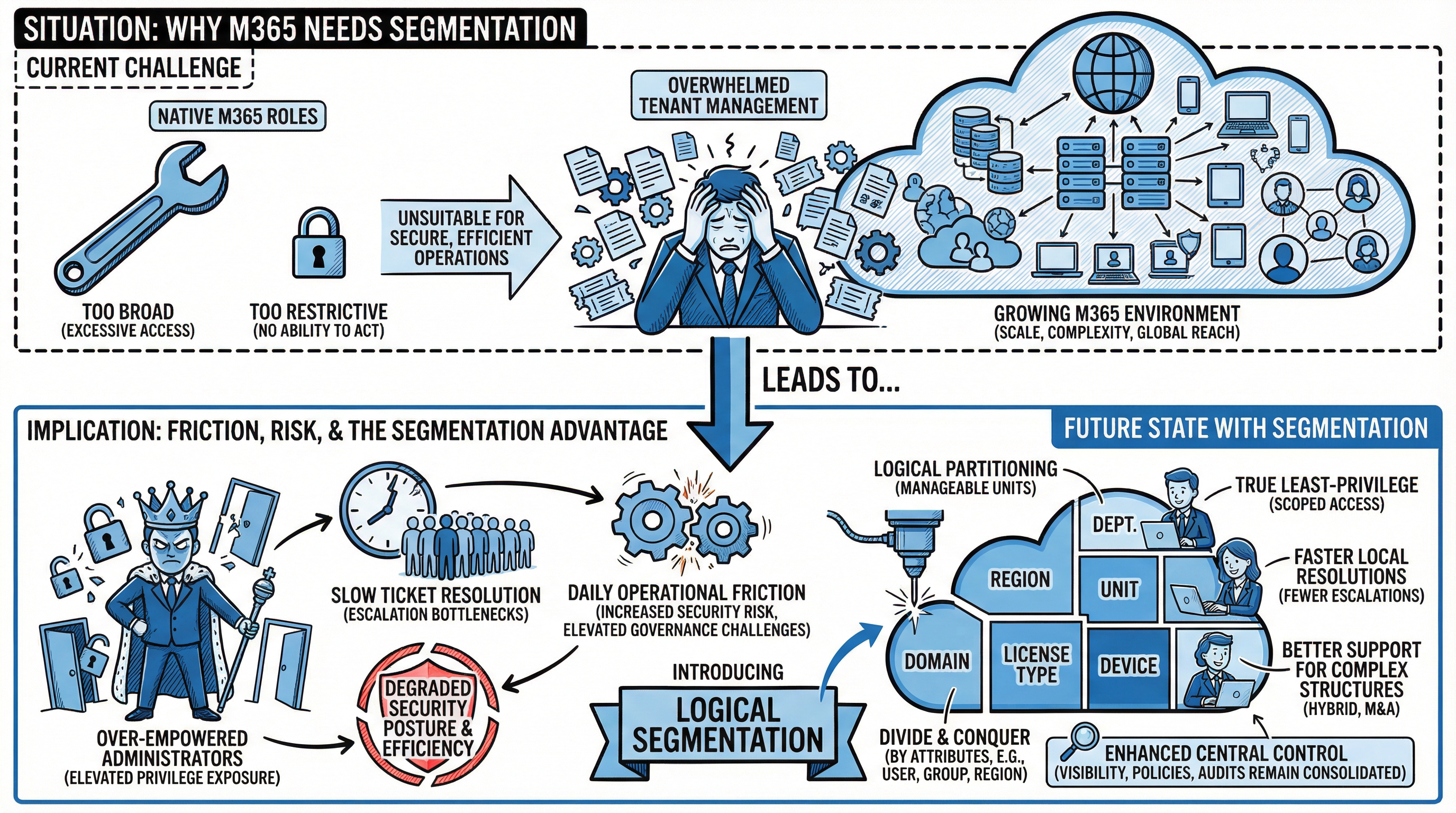
Native M365 roles lack precision - segmentation enables secure, least-privilege delegation across complex enterprise environments.

As Microsoft 365 environments grow in scale, complexity and global reach,traditional tenant management quickly becomes overwhelming. Native Microsoft365 roles are either too broad or too restrictive. The result? Over-empoweredadministrators, slow ticket resolution, and daily operational friction, all of which increase security risk and elevate governance challenges.
Modern enterprises need a way to divide and conquer that goes beyond Microsoft’s built-in capabilities. They need segmentation — the ability to logically partition a large tenant into smaller, manageable units that reflect their real organizational structure and governance needs. This is where advanced segmentation delivers meaningful operational and security value.
The limits of native Microsoft 365 delegation
Microsoft365 offers more than 120 built-in admin roles and a growing roster of permissions. But for large, distributed organisations, this is insufficient for true least-privilege delegation. The native approach forces two bad options:
Without finer control, admins in regional, departmental, or specialised teams end up with too much power or no ability to act at all -neither of which is suitable for secure, efficient operations.
Introducing logical segmentation for Microsoft 365
Logical segmentation lets organisations virtually slice their Microsoft 365 tenant based on business-relevant attributes. Think of it as creating focused operational “zones” within a larger estate, without spinning up multiple physical tenants.
This approach gives IT leaders the flexibility to:
What makes segmentation powerful is precision: access can be scoped with over 400 attributes, such as user, group, domain, device, license type or mailbox. So privileges are aligned with real business boundaries rather than generic,monolithic roles.
How segmentation reduces risk and boosts productivity
1. True Least-Privilege implementation
Rather than giving broad roles the ability to affect an entire tenant, segmentation ensures that each administrator can only act within their assigned virtual segment.This shrinks the potential blast radius of compromised credentials or privileged misuse.
2. Fewer escalations, faster resolutions
Delegating “just enough” access to local or departmental teams means fewer tickets hitting central IT. Routine tasks, such as user management, password resets, or license assignments, can be resolved immediately where the need arises.
3. Better support for complex organisational structures
Global companies with regional compliance requirements, hybrid work forces, or multiple subsidiaries benefit from segmentation that mirrors organisational realities without fragmenting the underlying tenant.
4. Mergers, acquisitions and tenant consolidation
When organisations merge tenants or integrate acquired environments, segmentation allows newly on boarded teams to operate securely without over-privileged access to the broader estate. This simplifies transitions and mitigates risk during vulnerable periods.
Segmentation does not replace central control - it enhances it
A segmented model does not decentralise governance. Instead, it enables central IT to retain visibility and control while distributing operational tasks safely. Policies, audits and oversight remain consolidated, and every segment is subject to the same overarching security and compliance frameworks. On-demand reporting and dashboards ensure that leadership still sees the full picture,even as tasks are delegated.
The bottom Line
As Microsoft 365 deployments scale, the one-tenant-fits-all model rapidly loses effectiveness. Without logical segmentation, security posture degrades and operational efficiency suffers.
Logical segmentation:
These benefits are not available with native Microsoft tools alone, making segmentation a powerful companion to Microsoft 365 governance and administration.
The national employment agency of France (France Travail) knew about the gaps.
They were documented in their own risk report.
They just never acted on them.
In the first quarter of 2024, three young hackers aged 21 to 23 used social engineering against an advisor at France Travail.
They obtained login credentials.
They gained access.
Because advisors had visibility into data across all citizens, not just those they served - the attackers accessed personal information belonging to 43 million people.
Names.
Addresses.
Phone numbers.
National identification numbers.
Data accumulated over more than 20 years.
In January2026, the French data protection authority, CNIL, issued its ruling.
The fine: approximately €5 million.
Not because the organization was hacked.
But because of three specific control failures - each already identified internally and left unresolved.
Failure one:
Access rights were too broad.
Advisors could view data far beyond their operational need.
Failure two:
There was no effective monitoring.
No logging capable of detecting abnormal behavior.
No alert when a single user accessed millions of records.
Failure three:
Authentication controls were insufficient.
Advisor accounts were not protected with robust multi-factor authentication
According to DLA Piper’s January 2026 GDPR report:
The pattern is clear.
Regulators do not primarily punish the attack. They punish the lack of control.
France Travail could confirm that the risks were known.
But they could not demonstrate that the controls were implemented.
That distinction mattered.
It cost them €5 million.
Concerned about excessive privilege, admin sprawl and slow support processes in your M365 environment? Contact us for a confidential review of delegation governance and segmentation strategy.
Strengthen your session and control framework - contact CySecPros for a confidential discussion.