Modern threats operate inside legitimate sessions - security must move from perimeter controls to in-session governance.

If you lead incident response at a global industrial enterprise, your reality looks like this:
Incidents are no longer contained to servers.
They begin in SaaS.
They spread through browser sessions.
They move laterally through identity and token reuse.
You are expected to restore operations fast.
Protect intellectual property.
Strengthen resilience.
Evaluate AI driven detection tools.
But here is the uncomfortable question:
How much visibility do you truly have inside active browser sessions?
For a Global Head of Incident Management responsible for continuity and cyber response, the challenge is not lack of tools.
It is blinds pots.
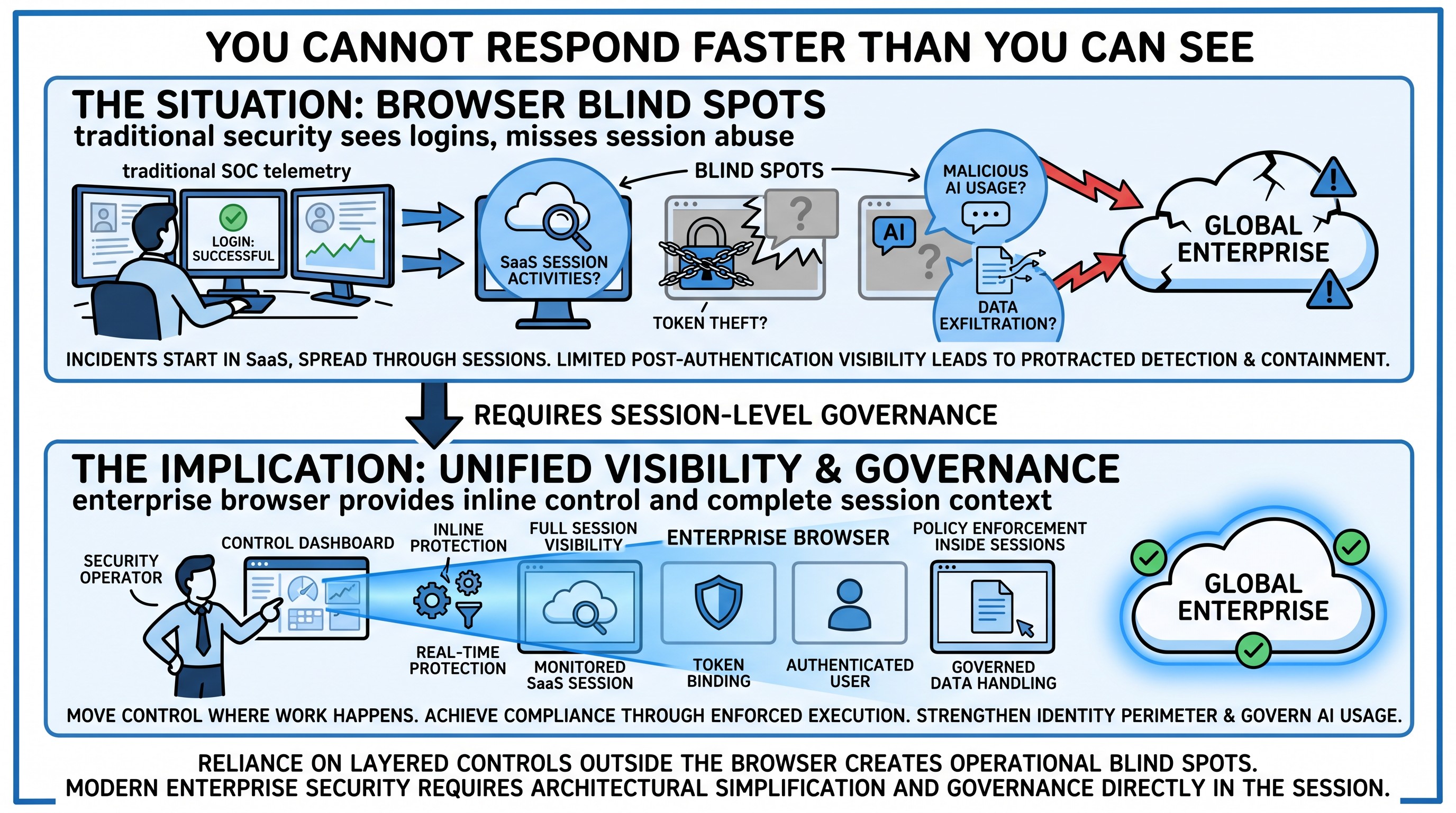
Most modern breaches operate inside authenticated sessions.
Token theft.
OAuth abuse.
Malicious extensions.
Prompt injection.
Traditional SOC telemetry often sees the login.
It does not see what happens next.
An enterprise browser changes that equation.
Session level visibility.
Token binding.
Extension control.
Inline protection before data leaves the session.
If your team is tasked with getting the organization back on track quickly, you need control where work happens.
The browser.
How are you currently detecting and containing session level compromise?
Compliance without control is paper security
For a cybersecurity officer responsible across multiple countries, operating under ISO 27001 and DORA, the challenge is different.
Compliance is measurable.
Audit evidence is required.
Access control must be demonstrable.
Third party exposure must be governed.
Acquisitions increase data sprawl.
Cloud migration increases identity complexity.
Phishing increases identity risk.
You may be working closely with SOC providers, Azure, Microsoft security stacks, Fortinet, Tenable, WAF solutions etc.
But ask yourself:
Can you enforce policy inside SaaS sessions?
Can you prove that sensitive data is not copied into unsanctioned AI tools?
Can you differentiate between corporate and personal tenants?
Can you restrict extension based attack vectors?
An enterprise browser does not replace your Microsoft ecosystem.
It strengthens it.
It embeds identity driven controls directly into web and SaaS workflows.
It enforces data handling rules in real time.
It provides audit logs across AI usage, prompts, and session behavior.
For a smaller IT organization, consolidation matters.
Fewer point solutions.
Unified policy.
Lower operational overhead.
How much of your compliance posture today depends on documentation rather than enforced execution?
Governance must follow AI
For leaders focused on risk and compliance, the challenge is not tactical detection.
It is governance.
Shadow AI is already present.
Employees use generative AI tools.
Data classification is incomplete.
Third party risk expands through SaaS ecosystems.
Policies alone do not prevent data from being pasted into AI prompts.
Visibility must exist before sensitive information leaves the browser.
An enterprise browser can redact sensitive data before it reaches AI providers.
Differentiate between personal and corporate AI usage.
Log AI interactions for audit and regulatory review.
Apply contextual policy based on identity and role.
If you are responsible for risk oversight and continuity, ask yourself:
How are you governing AI usage today?
Is it monitored?
Is it controlled?
Or is it assumed?
Identity is the new perimeter
For a CISO early in the journey of access and identity modernization, the priority is clarity.
You want to identify the right solutions quickly.
You want sustainable patch management.
You want proactive vulnerability reduction.
Identity risk is accelerating.
Phishing campaigns bypass MFA.
Session tokens are stolen.
Authenticated sessions are replayed.
Patch management is essential.
But what happens between patches?
What happens after authentication?
An enterprise browser binds SaaS sessions to managed environments.
Prevents token reuse outside approved context.
Restricts credential entry to sanctioned domains.
Enforces conditional access inside the session.
It complements identity governance platforms by strengthening the execution layer.
Identity policy without session enforcement leaves a gap.
How are you closing that gap today?
Strategy requires architectural change
For a CIO or CISO setting a new cybersecurity strategy, open to AI, open to new suppliers, open to modern architectures, the conversation shifts.
Security stacks have grown heavy.
VDI.
VPN.
CASB.
SWG.
Endpoint DLP.
Meanwhile, work lives in SaaS and AI enabled browsers.
The strategic shift is simple:
Move control to where work happens.
An enterprise browser embeds security directly into the workspace.
It reduces dependency on heavy infrastructure.
It simplifies governance.
It strengthens compliance posture.
It enables AI safely.
It is not another point solution.
It is architectural simplification.
When setting your next strategy, consider:
Are you adding more layers to compensate for browser blind spots?
Or are you modernizing the layer where risk now lives?
The provocative question
Across industrial enterprises.
Security service providers.
Banks.
Engineering firms.
The pattern is consistent.
Incidents increasingly originate inside legitimate sessions.
Compliance increasingly requires proof of execution, not documentation.
AI increasingly operates beyond traditional security visibility.
The enterprise browser introduces session level control, AI governance, identity enforcement, and unified visibility without fragmenting the stack further.
The question is not whether these challenges exist.
They do.
The question is how you are solving them today.
Are you relying on layered controls that operate outside the browser?
Or have you brought governance directly into the session itself?
That is the architectural decision that will define the next generation of enterprise security.
However, not all enterprise browsers are built equally. If you want to understand how to solve session-level security and AI governance challenges more effectively than traditional approaches, let us show you how we help you architect it right.
Strengthen your session and control framework - contact CySecPros for a confidential discussion.